4/26/20
How To Build A "Burner Device" For DEF CON In One Easy Step
TL;DR: Don't build a burner device. Probably this is not the risk you are looking for.
Introduction
Every year before DEF CON people starts to give advice to attendees to bring "burner devices" to DEF CON. Some people also start to create long lists on how to build burner devices, especially laptops. But the deeper we look into the topic, the more confusing it gets. Why are we doing this? Why are we recommending this? Are we focusing on the right things?
What is a "burner device" used for?
For starters, the whole "burner device" concept is totally misunderstood, even within the ITSEC community. A "burner device" is used for non-attribution. You know, for example, you are a spy and you don't want the country where you live to know that you are communicating with someone else. I believe this is not the situation for most attendees at DEF CON. More info about the meaning of "burner" https://twitter.com/Viss/status/877400669669306369
Burner phone means it has a throwaway SIM card with a throwaway phone, used for one specific operation only. You don't use the "burner device" to log in to your e-mail account or to VPN to your work or home.
But let's forget this word misuse issue for a moment, and focus on the real problem.
The bad advice
The Internet is full of articles focusing on the wrong things, especially when it comes to "burner devices". Like how to build a burner laptop, without explaining why you need it or how to use it.
The problem with this approach is that people end up "burning" (lame wordplay, sorry) significant resources for building a secure "burner device". But people are not educated about how they should use these devices.
The threats
I believe the followings are some real threats which are higher when you travel:
1. The laptop getting lost or stolen.
2. The laptop getting inspected/copied at the border.
These two risks have nothing to do with DEF CON, this is true for every travel.
Some other risks which are usually mentioned when it comes to "burner devices" and DEF CON:
3. Device getting owned via physical access while in a hotel room.
4. Network traffic Man-in-the-middle attacked. Your password displayed on a Wall of Sheep. Or having fun with Shellshock with DHCP. Information leak of NTLM hashes or similar.
5. Pwning the device via some nasty things like WiFi/TCP/Bluetooth/LTE/3G/GSM stack. These are unicorn attacks.
6. Pwning your device by pwning a service on your device. Like leaving your upload.php file in the root folder you use at CTFs and Nginx is set to autostart. The author of this article cannot comment on this incident whether it happened in real life or is just an imaginary example.
How to mitigate these risks?
Laptop getting stolen/lost/inspected at the border?
1. Bring a cheap, empty device with you. Or set up a fake OS/fake account to log in if you really need your day-to-day laptop. This dummy account should not decrypt the real files in the real account.
Device getting owned while in a hotel room with physical access
1. Don't bring any device with you.
2. If you bring any, make it tamper-resistant. How to do that depends on your enemy, but you can start by using nail glitter and Full Disk Encryption. Tools like Do Not Disturb help. It also helps if your OS supports suspending DMA devices before the user logs in.
3. If you can't make the device tamper-resistant, use a device that has a good defense against physical attackers, like iOS.
4. Probably you are not that important anyway that anyone will spend time and resources on you. If they do, probably you will only make your life miserable with all the hardening, but still, get pwned.
Network traffic Man-in-the-middle attacked
1. Don't bring any device with you.
2. Use services that are protected against MiTM. Like TLS.
3. Update your OS to the latest and greatest versions. Not everyone at DEF CON has a 0dayz worth of 100K USD, and even the ones who have won't waste it on you.
4. Use fail-safe VPN. Unfortunately, not many people talk about this or have proper solutions for the most popular operating systems.
5. For specific attacks like Responder, disable LLMNR, NBT-NS, WPAD, and IPv6 and use a non-work account on the machine. If you don't have the privileges to do so on your machine, you probably should not bring this device with you. Or ask your local IT to disable these services and set up a new account for you.
Pwning the device via some nasty thing like WiFi/TCP/Bluetooth/LTE/3G/GSM stack
1. Don't bring any device with you.
2. If you bring any, do not use this device to log in to work, personal email, social media, etc.
3. Don't worry, these things don't happen very often.
Pwning your device by pwning a service on your device
Just set up a firewall profile where all services are hidden from the outside. You rarely need any service accessible on your device at a hacker conference.
Conclusion
If you are still so afraid to go there, just don't go there. Watch the talks at home. But how is the hotel WiFi at a random place different from a hacker conference? Turns out, it is not much different, so you better spend time and resources on hardening your daily work devices for 365 days, instead of building a "burner device".
You probably need a "burner device" if you are a spy for a foreign government. Or you are the head of a criminal organization. Otherwise, you don't need a burner device. Maybe you need to bring a cheap replacement device.
Related newsDSniff
 "dsniff is a collection of tools for network auditing and penetration testing. dsniff, filesnarf, mailsnarf, msgsnarf, urlsnarf, and webspy passively monitor a network for interesting data (passwords, e-mail, files, etc.). arpspoof, dnsspoof, and macof facilitate the interception of network traffic normally unavailable to an attacker (e.g, due to layer-2 switching). sshmitm and webmitm implement active monkey-in-the-middle attacks against redirected SSH and HTTPS sessions by exploiting weak bindings in ad-hoc PKI." read more...
"dsniff is a collection of tools for network auditing and penetration testing. dsniff, filesnarf, mailsnarf, msgsnarf, urlsnarf, and webspy passively monitor a network for interesting data (passwords, e-mail, files, etc.). arpspoof, dnsspoof, and macof facilitate the interception of network traffic normally unavailable to an attacker (e.g, due to layer-2 switching). sshmitm and webmitm implement active monkey-in-the-middle attacks against redirected SSH and HTTPS sessions by exploiting weak bindings in ad-hoc PKI." read more...Website: http://www.monkey.org/~dugsong/dsniff/
FOOTPRITING AND INFORMATION GATHERING USED IN HACKING
WHAT IS FOOTPRITING AND INFORMATION GATHERING IN HACKING?
Footpriting is the technique used for gathering information about computer systems and the entities they belongs too.
To get this information, a hacker might use various tools and technologies.
Basically it is the first step where hacker gather as much information as possible to find the way for cracking the whole system or target or atleast decide what types of attacks will be more suitable for the target.
Footpriting can be both passive and active.
Reviewing a company's website is an example of passive footprinting,
whereas attempting to gain access to sensititve information through social engineering is an example of active information gathering.
During this phase hacking, a hacker can collect the following information>- Domain name
-IP Addresses
-Namespaces
-Employee information
-Phone numbers
-E-mails
Job information
Tip-You can use http://www.whois.com/ website to get detailed information about a domain name information including its owner,its registrar, date of registration, expiry, name servers owner's contact information etc.
Use of Footprinting & Information Gathering in People Searching-
Now a days its very easy to find anyone with his/her full name in social media sites like Facebook, Instragram,Twitter,Linkdedin to gather information about date of birth,birthplace, real photos, education detail, hobbies, relationship status etc.
There are several sites like PIPL,PeekYou, Transport Sites such as mptransport,uptransport etc and Job placement Sites such as Shine.com,Naukari.com , Monster.com etc which are very useful for hacker to collect information about anyone.
Hacker collect the information about you from your Resume which you uploaded on job placement site for seeking a job as well as hacker collect the information from your vehicle number also from transport sites to know about the owner of vehicle, adderess etc then after they make plan how to attack on victim to earn money after know about him/her from collecting information.
INFORMATION GATHERING-It is the process of collecting the information from different places about any individual company,organization, server, ip address or person.
Most of the hacker spend his time in this process.
Information gathering plays a vital role for both investigating and attacking purposes.This is one of the best way to collect victim data and find the vulnerability and loopholes to get unauthorized modifications,deletion and unauthorized access.
Footpriting is the technique used for gathering information about computer systems and the entities they belongs too.
To get this information, a hacker might use various tools and technologies.
Basically it is the first step where hacker gather as much information as possible to find the way for cracking the whole system or target or atleast decide what types of attacks will be more suitable for the target.
Footpriting can be both passive and active.
Reviewing a company's website is an example of passive footprinting,
whereas attempting to gain access to sensititve information through social engineering is an example of active information gathering.
During this phase hacking, a hacker can collect the following information>- Domain name
-IP Addresses
-Namespaces
-Employee information
-Phone numbers
-E-mails
Job information
Tip-You can use http://www.whois.com/ website to get detailed information about a domain name information including its owner,its registrar, date of registration, expiry, name servers owner's contact information etc.
Use of Footprinting & Information Gathering in People Searching-
Now a days its very easy to find anyone with his/her full name in social media sites like Facebook, Instragram,Twitter,Linkdedin to gather information about date of birth,birthplace, real photos, education detail, hobbies, relationship status etc.
There are several sites like PIPL,PeekYou, Transport Sites such as mptransport,uptransport etc and Job placement Sites such as Shine.com,Naukari.com , Monster.com etc which are very useful for hacker to collect information about anyone.
Hacker collect the information about you from your Resume which you uploaded on job placement site for seeking a job as well as hacker collect the information from your vehicle number also from transport sites to know about the owner of vehicle, adderess etc then after they make plan how to attack on victim to earn money after know about him/her from collecting information.
INFORMATION GATHERING-It is the process of collecting the information from different places about any individual company,organization, server, ip address or person.
Most of the hacker spend his time in this process.
Information gathering plays a vital role for both investigating and attacking purposes.This is one of the best way to collect victim data and find the vulnerability and loopholes to get unauthorized modifications,deletion and unauthorized access.
More info
4/25/20
How To Hack Any Game On Your Android Smartphone

How To Hack Any Game On Your Android Smartphone
By hacking android game you can unlock all the levels, use any resource according to your wish and lots more. Proceed with the method shown below to hack any game on your Android. But sometimes while playing our favorite game we get short on our resources that are needed to play that game, like power, weapons or lives etc. That consequence really becomes bothersome, so to overcome this we are here with the trick How To Hack Any Game On Android.
Today millions of character are using the android phone. Now an Android device enhances significant part of our life. Everyone loves to play games on their android device. There are lots of cool games that are today available on your Android device in Google Play Store.
How To Hack Any Game On Android 2018
Now it's time to hack into the game and use any resources that you want to play at any level of the game. The method is really working and will let you alter the game according to your wish. Just proceed with simple steps below.
Steps To Hack Any Game On Android
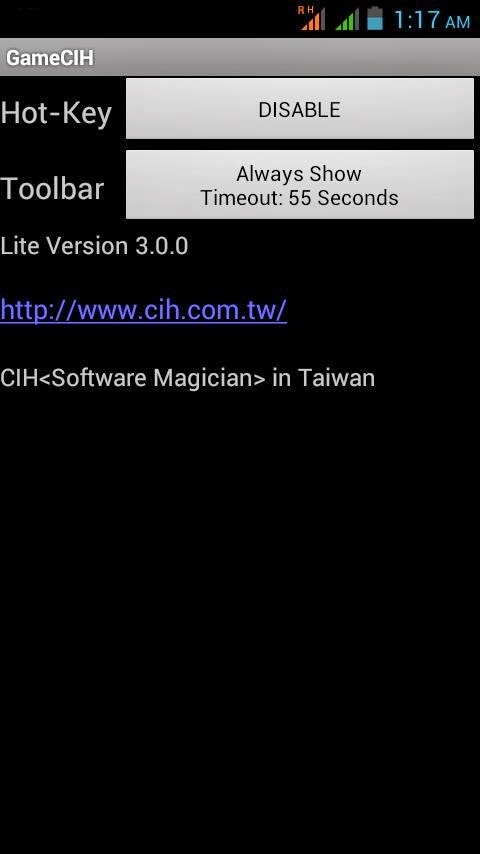
Step 1. First of all after rooting your android device open the GameCIH App. It will ask you for superuser access, grant it.(This will only come if you have properly rooted your android device. Now on the home screen of this app, you will see Hot-Key option, select any of them which you feel more convenient while using in your android.
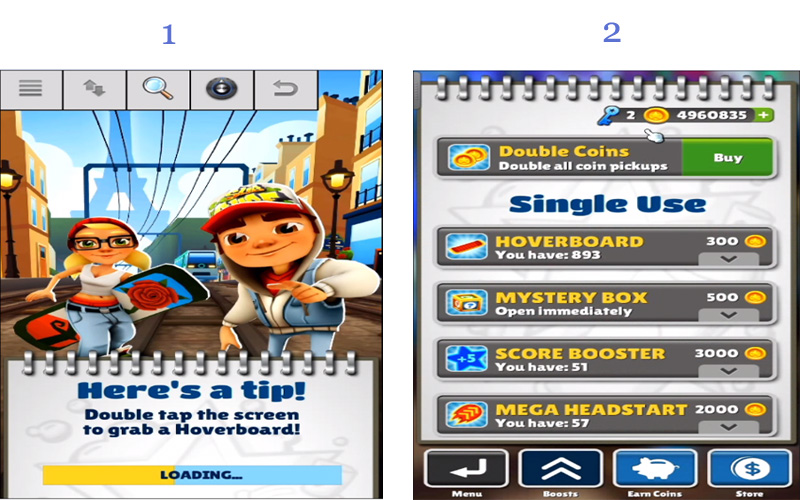
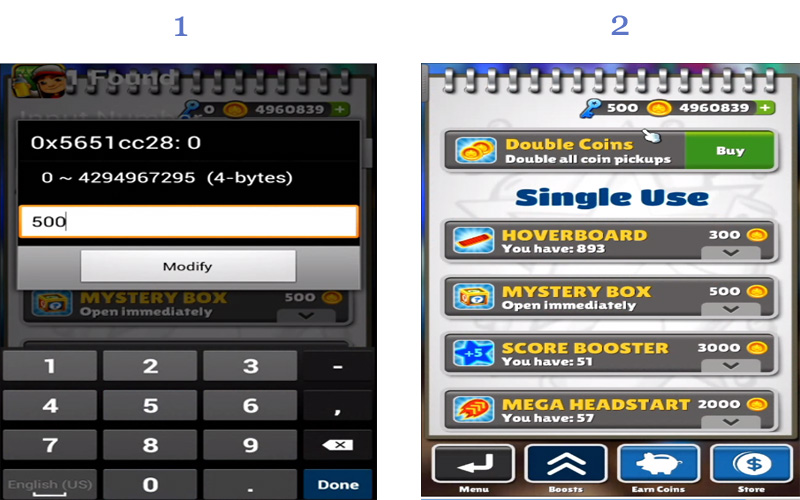
Step 2. Now open the game that you want to hack into your android device. Now pause the game and access the hotkeys displaying there, select any value that you want to edit in your game. Like any of text value like keys of subway surfer game.
Step 3. Enter your desired value in the text field box appeared there and click on done. Now you will see default value will get replaced with your value. Similarly, you can alter any values in any of the game according to your wish.
That's it game hacking is done, Now you can access any resources using this hack.
So above is all about Hack Any Game On Android. With the help of this trick, you can alter any coins, lives, money, weapons power and lots more in any of your favorite android game and can enjoy the unlimited game resources according to your wish.
Using Game Guardian
Game Guardian Apk is one of the best apps which you can have on your Android smartphone. With the help of this app, you can easily get unlimited coins, gems and can perform all other hacks. However, Game Guardian Apk needs a rooted Android smartphone to work. Here's a simple guide that will help you.
Step 1. First of all, you need to download the latest version of Game Guardian on your Android smartphone from the given download link above or below.
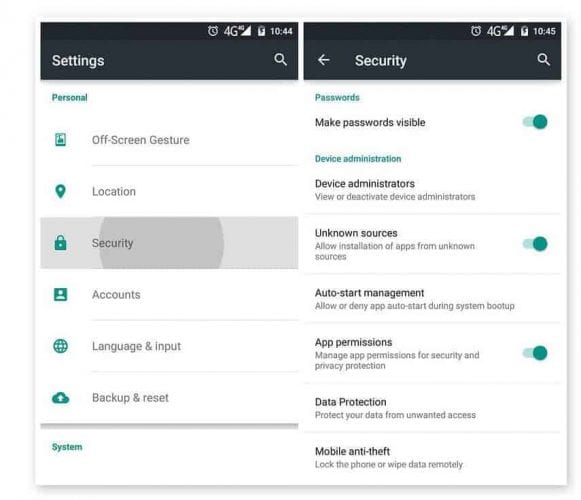
Step 2. After downloading on your smartphone, you need to enable the Unknown Source on your device. For that, you need to visit Settings > Security > Unknown Sources
Step 3. Now install the app and then press the home button to minimize the app. Now open any game that you want to hack. You will see an overlay of Game Guardian App icon. Tap on it.
Step 4. Now you need to tap on the Search Button and set the value. If you don't know the values, then simply set it to auto.
Step 5. You need to search for the value which you want to hack like money, gem, health, score etc. You can change all those values. Suppose, if you need to decrease the number of values, you need to scan again for the new value.
Step 6. Finally, you need to select all the values and then change it to infinite numbers like '9999999' or whatever you want.
That's it, you are done! This is how you can use Game Guardian Apk to hack games on your Android smartphone.
With this, you can play a game at any levels without any shortage of any resource that can interrupt your gameplay. Hope you like this coolest android game hack. Don't forget to share it with others too.
Related links
4/23/20
USE OF CRYPTOGRAPHY IN HACKING
WHAT IS CRYPTOGRAPHY?
OR
Cryptography is a method of protecting information and communication through the use of codes so that only those whom the information is intended can read and process it.
Information plays a vital role in running of business and organizations etc, information in the wrong hands can leads to loss of business.
To secure communication organizations use cryptology to cipher information .
Read moreThe process of transforming information into nonhuman readable form or vice versa is called cryptography.
Cryptography is the science of ciphering and deciphering messages.
OR
Cryptography is a method of protecting information and communication through the use of codes so that only those whom the information is intended can read and process it.
In Computer Science, cryptography refers to secure information and communication techniques derived from mathematical concepts , a set of rule based calculations called algorithm to transform message in ways the hard to readable for human.
Information plays a vital role in running of business and organizations etc, information in the wrong hands can leads to loss of business.
To secure communication organizations use cryptology to cipher information .
Support For XXE Attacks In SAML In Our Burp Suite Extension
In this post we present the new version of the Burp Suite extension EsPReSSO - Extension for Processing and Recognition of Single Sign-On Protocols. A DTD attacker was implemented on SAML services that was based on the DTD Cheat Sheet by the Chair for Network and Data Security (https://web-in-security.blogspot.de/2016/03/xxe-cheat-sheet.html). In addition, many fixes were added and a new SAML editor was merged. You can find the newest version release here: https://github.com/RUB-NDS/BurpSSOExtension/releases/tag/v3.1
New SAML editor
Before the new release, EsPReSSO had a simple SAML editor where the decoded SAML messages could be modified by the user. We extended the SAML editor so that the user has the possibility to define the encoding of the SAML message and to select their HTTP binding (HTTP-GET or HTTP-POST). |
| Redesigned SAML Encoder/Decoder |
Enhancement of the SAML attacker
XML Signature Wrapping and XML Signature Faking attacks have already been part of the previous EsPReSSO version. Now the user can also perform DTD attacks! The user can select from 18 different attack vectors and manually refine them all before applying the change to the original message. Additional attack vectors can also be added by extending the XML config file of the DTD attacker.The DTD attacker can also be started in a fully automated mode. This functionality is integrated in the BurpSuite Intruder.
 |
| DTD Attacker for SAML messages |
Supporting further attacks
We implemented a CertificateViewer which extracts and decodes the certificates contained within the SAML tokens. In addition, a user interface for executing SignatureExclusion attack on SAML has been implemented.Additional functions will follow in later versions.
Currently we are working on XML Encryption attacks.This is a combined work from Nurullah Erinola, Nils Engelbertz, David Herring, Juraj Somorovsky, and Vladislav Mladenov.
The research was supported by the European Commission through the FutureTrust project (grant 700542-Future-Trust-H2020-DS-2015-1).
Related word
4/22/20
Testing SAML Endpoints For XML Signature Wrapping Vulnerabilities
A lot can go wrong when validating SAML messages. When auditing SAML endpoints, it's important to look out for vulnerabilities in the signature validation logic. XML Signature Wrapping (XSW) against SAML is an attack where manipulated SAML message is submitted in an attempt to make the endpoint validate the signed parts of the message -- which were correctly validated -- while processing a different attacker-generated part of the message as a way to extract the authentication statements. Because the attacker can arbitrarily forge SAML assertions which are accepted as valid by the vulnerable endpoint, the impact can be severe. [1,2,3]
Testing for XSW vulnerabilities in SAML endpoints can be a tedious process, as the auditor needs to not only know the details of the various XSW techniques, but also must handle a multitude of repetitive copy-and-paste tasks and apply the appropriate encoding onto each message. The latest revision of the XSW-Attacker module in our BurpSuite extension EsPReSSo helps to make this testing process easier, and even comes with a semi-automated mode. Read on to learn more about the new release!
To simplify its use, the XSW-Attacker performs the attack in a two step process of initialization and execution, as reflected by its two tabs Init Attack and Execute Attack. The interface of the XSW-Attacker is depicted below.
The Init Attack tab displays the current SAML message. To execute a signature wrapping attack, a payload needs to be configured in a way that values of the originally signed message are replaced with values of the attacker's choice. To do this, enter the value of a text-node you wish to replace in the Current value text-field. Insert the replacement value in the text-field labeled New value and click the Add button. Multiple values can be provided; however, all of which must be child nodes of the signed element. Valid substitution pairs and the corresponding XPath selectors are displayed in the Modifications Table. To delete an entry from the table, select the entry and press `Del`, or use the right-click menu.
Next, click the Generate vectors button - this will prepare the payloads accordingly and brings the Execute Attack tab to the front of the screen.
At the top of the Execute Attack tab, select one of the pre-generated payloads. The structure of the selected vector is explained in a shorthand syntax in the text area below the selector.
The text-area labeled Attack vector is editable and can be used to manually fine-tune the chosen payload if necessary. The button Pretty print opens up a syntax-highlighted overview of the current vector.
To submit the manipulated SAML response, use Burp's Forward button (or Go, while in the Repeater).
First, open an intercepted request in Burp's Intruder (e.g., by pressing `Ctrl+i`). For the attack type, select Sniper. Open the Intruder's Positions tab, clear all payload positions but the value of the XML message (the `SAMLResponse` parameter, in our example). Note: the XSW-Attacker can only handle XML messages that contain exactly one XML Signature.
Next, switch to the Payloads tab and for the Payload Type, select Extension-generated. From the newly added Select generator drop-down menu, choose XSW Payloads, as depicted in the screenshot below.
While still in the Payloads tab, disable the URL-encoding checkbox in the Payload Encoding section, since Burp Intruder deals with the encoding automatically and should suffice for most cases.
Click the Start Attack button and a new window will pop up. This window is shown below and is similar to the XSW Attacker's Init Attack tab.
Configure the payload as explained in the section above. In addition, a schema analyzer can be selected and checkboxes at the bottom of the window allow the tester to choose a specific encoding. However, for most cases the detected presets should be correct.
Click the Start Attack button and the Intruder will start sending each of the pre-generated vectors to the configured endpoint. Note that this may result in a huge number of outgoing requests. To make it easier to recognize the successful Signature Wrapping attacks, it is recommended to use the Intruder's Grep-Match functionality. As an example, consider adding the replacement values from the Modifications Table as a Grep-Match rule in the Intruder's Options tab. By doing so, a successful attack vector will be marked with a checkmark in the results table, if the response includes any of the configure grep rules.
Our students Nurullah Erinola, Nils Engelberts and David Herring did a great job improving the execution of XSW and implementing a much better UI.
---
[1] On Breaking SAML - Be Whoever You Want to Be
[2] Your Software at My Service
[3] Security Analysis of XAdES Validation in the CEF Digital Signature Services (DSS)
[4] WS-Attacker
Related linksTesting for XSW vulnerabilities in SAML endpoints can be a tedious process, as the auditor needs to not only know the details of the various XSW techniques, but also must handle a multitude of repetitive copy-and-paste tasks and apply the appropriate encoding onto each message. The latest revision of the XSW-Attacker module in our BurpSuite extension EsPReSSo helps to make this testing process easier, and even comes with a semi-automated mode. Read on to learn more about the new release!
SAML XSW-Attacker
After a signed SAML message has been intercepted using the Burp Proxy and shown in EsPReSSO, you can open the XSW-Attacker by navigating to the SAML tab and then the Attacker tab. Select Signature Wrapping from the drop down menu, as shown in the screenshot below:To simplify its use, the XSW-Attacker performs the attack in a two step process of initialization and execution, as reflected by its two tabs Init Attack and Execute Attack. The interface of the XSW-Attacker is depicted below.
 |
| XSW-Attacker overview |
The Init Attack tab displays the current SAML message. To execute a signature wrapping attack, a payload needs to be configured in a way that values of the originally signed message are replaced with values of the attacker's choice. To do this, enter the value of a text-node you wish to replace in the Current value text-field. Insert the replacement value in the text-field labeled New value and click the Add button. Multiple values can be provided; however, all of which must be child nodes of the signed element. Valid substitution pairs and the corresponding XPath selectors are displayed in the Modifications Table. To delete an entry from the table, select the entry and press `Del`, or use the right-click menu.
Next, click the Generate vectors button - this will prepare the payloads accordingly and brings the Execute Attack tab to the front of the screen.
At the top of the Execute Attack tab, select one of the pre-generated payloads. The structure of the selected vector is explained in a shorthand syntax in the text area below the selector.
The text-area labeled Attack vector is editable and can be used to manually fine-tune the chosen payload if necessary. The button Pretty print opens up a syntax-highlighted overview of the current vector.
To submit the manipulated SAML response, use Burp's Forward button (or Go, while in the Repeater).
Automating XSW-Attacker with Burp Intruder
Burp's Intruder tool allows the sending of automated requests with varying payloads to a test target and analyzes the responses. EsPReSSO now includes a Payload Generator called XSW Payloads to facilitate when testing the XML processing endpoints for XSW vulnerabilities. The following paragraphs explain how to use the automated XSW attacker with a SAML response.First, open an intercepted request in Burp's Intruder (e.g., by pressing `Ctrl+i`). For the attack type, select Sniper. Open the Intruder's Positions tab, clear all payload positions but the value of the XML message (the `SAMLResponse` parameter, in our example). Note: the XSW-Attacker can only handle XML messages that contain exactly one XML Signature.
Next, switch to the Payloads tab and for the Payload Type, select Extension-generated. From the newly added Select generator drop-down menu, choose XSW Payloads, as depicted in the screenshot below.
While still in the Payloads tab, disable the URL-encoding checkbox in the Payload Encoding section, since Burp Intruder deals with the encoding automatically and should suffice for most cases.
Click the Start Attack button and a new window will pop up. This window is shown below and is similar to the XSW Attacker's Init Attack tab.
Configure the payload as explained in the section above. In addition, a schema analyzer can be selected and checkboxes at the bottom of the window allow the tester to choose a specific encoding. However, for most cases the detected presets should be correct.
Click the Start Attack button and the Intruder will start sending each of the pre-generated vectors to the configured endpoint. Note that this may result in a huge number of outgoing requests. To make it easier to recognize the successful Signature Wrapping attacks, it is recommended to use the Intruder's Grep-Match functionality. As an example, consider adding the replacement values from the Modifications Table as a Grep-Match rule in the Intruder's Options tab. By doing so, a successful attack vector will be marked with a checkmark in the results table, if the response includes any of the configure grep rules.
Credits
EsPReSSO's XSW Attacker is based on the WS-Attacker [4] library by Christian Mainka and the original adoption for EsPReSSO has been implemented by Tim Günther.Our students Nurullah Erinola, Nils Engelberts and David Herring did a great job improving the execution of XSW and implementing a much better UI.
---
[1] On Breaking SAML - Be Whoever You Want to Be
[2] Your Software at My Service
[3] Security Analysis of XAdES Validation in the CEF Digital Signature Services (DSS)
[4] WS-Attacker
BurpSuite Introduction & Installation
What is BurpSuite?
Burp Suite is a Java based Web Penetration Testing framework. It has become an industry standard suite of tools used by information security professionals. Burp Suite helps you identify vulnerabilities and verify attack vectors that are affecting web applications. Because of its popularity and breadth as well as depth of features, we have created this useful page as a collection of Burp Suite knowledge and information.
In its simplest form, Burp Suite can be classified as an Interception Proxy. While browsing their target application, a penetration tester can configure their internet browser to route traffic through the Burp Suite proxy server. Burp Suite then acts as a (sort of) Man In The Middle by capturing and analyzing each request to and from the target web application so that they can be analyzed.
Everyone has their favorite security tools, but when it comes to mobile and web applications I've always found myself looking BurpSuite . It always seems to have everything I need and for folks just getting started with web application testing it can be a challenge putting all of the pieces together. I'm just going to go through the installation to paint a good picture of how to get it up quickly.
BurpSuite is freely available with everything you need to get started and when you're ready to cut the leash, the professional version has some handy tools that can make the whole process a little bit easier. I'll also go through how to install FoxyProxy which makes it much easier to change your proxy setup, but we'll get into that a little later.
Requirements and assumptions:
Mozilla Firefox 3.1 or Later Knowledge of Firefox Add-ons and installation The Java Runtime Environment installed
Download BurpSuite from http://portswigger.net/burp/download.htmland make a note of where you save it.
on for Firefox from https://addons.mozilla.org/en-US/firefox/addon/foxyproxy-standard/
If this is your first time running the JAR file, it may take a minute or two to load, so be patient and wait.
Video for setup and installation.
You need to install compatible version of java , So that you can run BurpSuite.
Related word
Web-fu - The Ultimate Web Hacking Chrome Extension
Web-fu Is a web hacking tool focused on discovering and exploiting web vulnerabilitites.
BROWSER INTEGRATION
This tool has many advantages, as a browser-embedded webhacking tool, is very useful for scanning browser-authenticated applications, if browser can authenticate and access to the web application, the tool also can. Note that some other tools do not support neither certificate authentication nor web vpn accesses.
The integration with chrome, provides a more comfortable and agile way of web-hacking, and you have all the application data loaded on the hacking tool, you don't need to copy the url, cookies, etc. to the tool, just right click and hack.
The browser rendering engine is also used in this tool, to draw the html of the responses.
FALSES POSITIVES
When I coded this tool, I was obsessed with false positives, which is the main problem in all detection tools. I have implemented a gauss algorithm, to reduce the faslse positives automatically which works very very well, and save a lot of time to the pentester.
VIDEO
Here is a video, with some of the web-fu functionalitites:
VISUAL FEATURES
This tool has a visual crawler. Normal crawlers doesn't parse the ajvascript, this tool does. The visual crawler loads each link of the web site, rendering the html and executing all the javascript as a normal load, then the links are processed from he DOM and clicked.
A visual form cracker, is also available, althow is experimental and only works on some kind of forms.
SCANNING FEATURES
The web-fu's portscanner, has a database of a common web ports, like 80,81,8080 and so on.
The cracker module, can bruteforce web directories to find new attack vectors, and can fuzz get and post parameters for discovering vulns, and also crack passwords. There are 9 preloaded wordlists, and you can also load a custom wordlist. Prefilters, falsepositive reductor and render will be helpful. The scanners support SSL, if the website can be loaded in the chrome, can be scanned by web-fu.
ENCODERS & DECODERS
The supported encoders and decoders are: base64, urlescape and urlencode
OTHER FEATURES
A web notepad is available, saving the information on the browser localStorage, there is one notepad per site. A cookie editor is also very useful for pentesting. The inteceptor, is like a web proxy but from the inside of the browser, you can intercept a request There is also a session locker and a exploit web search.
CHROME STORE
Here is the link to the chrome store, the prize is about one euro, very cheap if you compare with other scanners: Web-Fu on Chrome Store
With webfu, you will do the best web site pentest and vulnerability assessment.
Related articles
BROWSER INTEGRATION
This tool has many advantages, as a browser-embedded webhacking tool, is very useful for scanning browser-authenticated applications, if browser can authenticate and access to the web application, the tool also can. Note that some other tools do not support neither certificate authentication nor web vpn accesses.
The integration with chrome, provides a more comfortable and agile way of web-hacking, and you have all the application data loaded on the hacking tool, you don't need to copy the url, cookies, etc. to the tool, just right click and hack.
The browser rendering engine is also used in this tool, to draw the html of the responses.
FALSES POSITIVES
When I coded this tool, I was obsessed with false positives, which is the main problem in all detection tools. I have implemented a gauss algorithm, to reduce the faslse positives automatically which works very very well, and save a lot of time to the pentester.
VIDEO
Here is a video, with some of the web-fu functionalitites:
VISUAL FEATURES
This tool has a visual crawler. Normal crawlers doesn't parse the ajvascript, this tool does. The visual crawler loads each link of the web site, rendering the html and executing all the javascript as a normal load, then the links are processed from he DOM and clicked.
A visual form cracker, is also available, althow is experimental and only works on some kind of forms.
SCANNING FEATURES
The web-fu's portscanner, has a database of a common web ports, like 80,81,8080 and so on.
The cracker module, can bruteforce web directories to find new attack vectors, and can fuzz get and post parameters for discovering vulns, and also crack passwords. There are 9 preloaded wordlists, and you can also load a custom wordlist. Prefilters, falsepositive reductor and render will be helpful. The scanners support SSL, if the website can be loaded in the chrome, can be scanned by web-fu.
ENCODERS & DECODERS
The supported encoders and decoders are: base64, urlescape and urlencode
OTHER FEATURES
A web notepad is available, saving the information on the browser localStorage, there is one notepad per site. A cookie editor is also very useful for pentesting. The inteceptor, is like a web proxy but from the inside of the browser, you can intercept a request There is also a session locker and a exploit web search.
CHROME STORE
Here is the link to the chrome store, the prize is about one euro, very cheap if you compare with other scanners: Web-Fu on Chrome Store
With webfu, you will do the best web site pentest and vulnerability assessment.
Related articles
4/21/20
CEH Practical: Gathering Target Information: Reconnaissance And Competitive Intelligence
CEH Exam Objectives:
Describe Reconnaissance.
Describe aggressive/competitive intelligence.
Reconnaissance
Reconnaissance is the process of gathering informative data about a particular target of a malicious hack by exploring the targeted system. Basically two types of Reconnaissance exist i.e. Active and Passive. Active reconnaissance typically related to port scanning and observing the vulnerabilities about the targeted system (i.e., which ports are left vulnerable and/or if there are ways around the firewall and routers). Passive reconnaissance typically you will not be directly connected to a computer system. This process is used to gather essential information without ever interacting with the target systems.Understand Aggressive Intelligence
Competitive intelligence means information gathering about competitors' products, marketing, and technologies. Most competitive intelligence is non intrusive to the company being investigated and is benign in nature. It's used for product comparison or as a sales and marketing tactic to better understand how competitors are positioning their products or services.Online tools to gather competitive intelligence
Exercise 1.1
Using KeywordSpy
To use the KeywordSpy online tool to gather competitive intelligence information:- Go to the www.keywordspy.com website and enter the website address of the target in the search field
- Review the report and determine valuable keywords, links, or other information.
Exercise 1.2
Using spyfu
- Go to your browser and type www.spyfu.com and enter the website address of the target in the search field.
Exercise 1.3
Using the EDGAR Database to Gather Information
1. Determine the company's stock symbol using Google.
2. Open a web browser to www.sec.gov.
3. On the right side of the page, click the link EDGAR Filers.
2. Open a web browser to www.sec.gov.
3. On the right side of the page, click the link EDGAR Filers.
4. Click the Search For Filings menu and enter the company name or stock symbol to search the filings for information. You can learn, for example, where the company is registered and who reported the filing.
5. Use the Yahoo! yellow pages ( http://yp.yahoo.com ) to see if an address or phone number is listed for any of the employee names you have located.
5. Use the Yahoo! yellow pages ( http://yp.yahoo.com ) to see if an address or phone number is listed for any of the employee names you have located.
Related news
Subscribe to:
Posts (Atom)